Monday, April 26, 2021, I have attended the event Intro to Hacking: Open Source Intelligence organised by Woman who code New York.
Open Source Intelligence (OSINT) is the practice of gathering information from published or publicly available sources. Indeed, Open source intelligence (OSINT) is a method of using open source tools to collect information from publicly available sources and then analyse it in order to make a decision or take some action. OSINT can be helpful in the right hands, but harmful when hackers use it to learn more about your organisation.
What tells Wikipedia about Open Source Intelligence is:
OSINT is defined by both the U.S. Director of National Intelligence and the U.S. Department of Defense (DoD), as intelligence «produced from publicly available information that is collected, exploited, and disseminated in a timely manner to an appropriate audience for the purpose of addressing a specific intelligence requirement.» As defined by NATO, OSINT is intelligence «derived from publicly available information, as well as other unclassified information that has limited public distribution or access.»
The first step is collecting information. Tools such as Shodan or VPN Hunter, can highlight and identify an organisation’s Web servers, mail servers, remote access endpoints and many other Internet-facing devices.
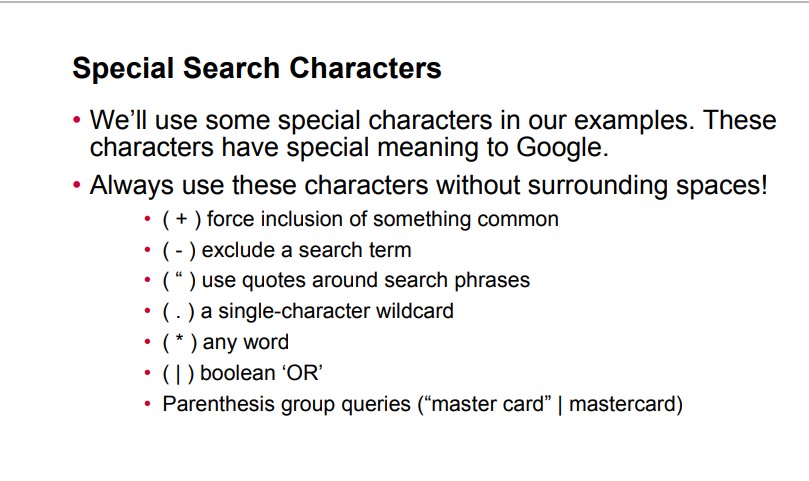
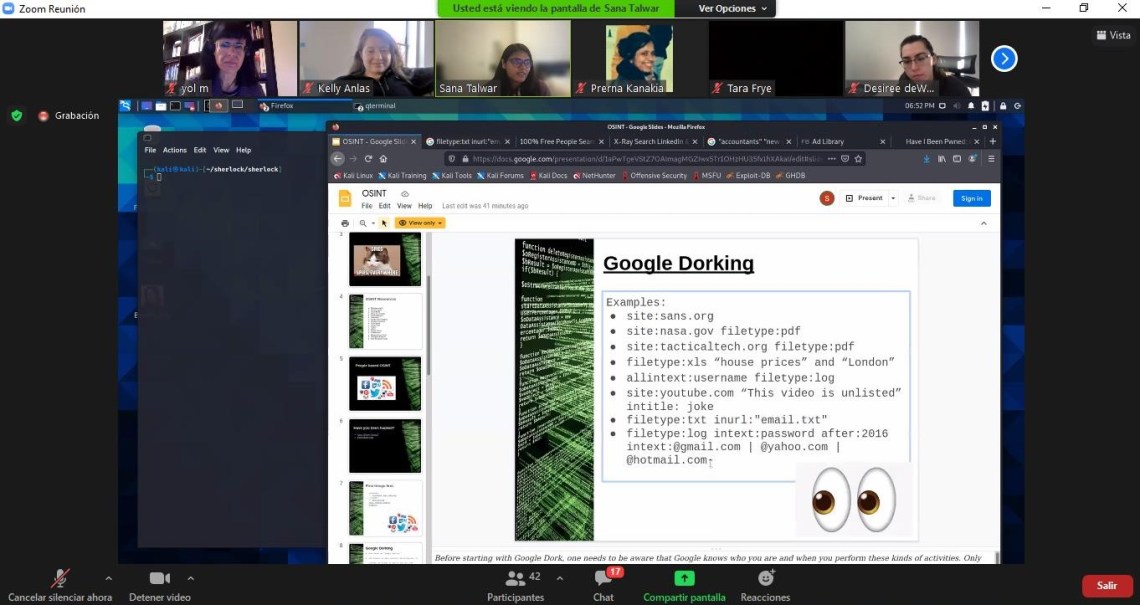
Once the systems have been identified, the Google Hacking Database (GHDB) can be used to detect vulnerabilities within systems without actually coming in contact with them. GHDB contains hundreds of “Google dorks” (search terms which can be used to identify system vulnerabilities from their cached Google pages), which can be accessed with a handy search function.
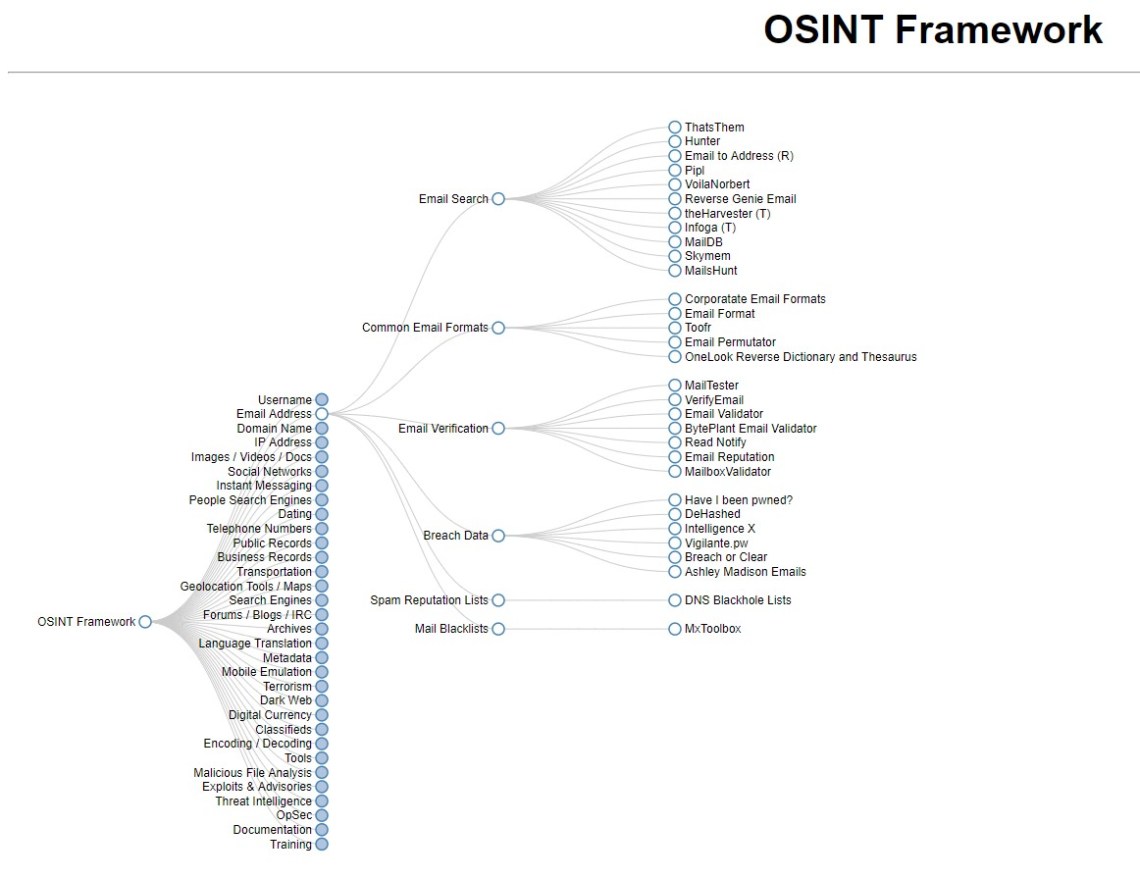
One interesting tool to collect data is The OSINT Framework a visually-represented collection of what data is able to be collected and by which tools.
Other note I think is useful to non-tech specialist is:
I have other interesting information to share of this event, and I am working in it as it can be understand by non-tech people to be useful for them.
And remember, you need to be aware of what kind of information is publicly available to best protect yourself and/or your organization.
More information in the following articles:
FORBES’s article about the searching tool Maltego: When Everyone Can Mine Your Data
An Introduction To Open Source Intelligence (OSINT) Gathering
 Contenido Web de Yolanda Muriel está sujeto bajo Licencia Creative Commons Atribución-NoComercial-SinDerivadas 3.0 Unported.
Contenido Web de Yolanda Muriel está sujeto bajo Licencia Creative Commons Atribución-NoComercial-SinDerivadas 3.0 Unported.

1 comentario